Introduction: Convenience Meets Cyber Risk
In the modern digital workplace, productivity tools have become as essential as email. Among them, Notion stands out as a powerful all-in-one platform for notes, project management, documentation, and collaboration. Millions of users log in daily to organize their work and personal lives. However, with popularity comes risk. A simple search or click related to Notion login can expose users to serious cybersecurity threats if they are not careful.
This article explores why the phrase “Notion login” has become a high-risk entry point for cybercriminal activity, how attackers exploit user behavior, and what practical steps you can take to protect your data, identity, and organization. Understanding these dangers is no longer optional—it is a necessity in today’s threat landscape.
Understanding Notion and Its Widespread Use
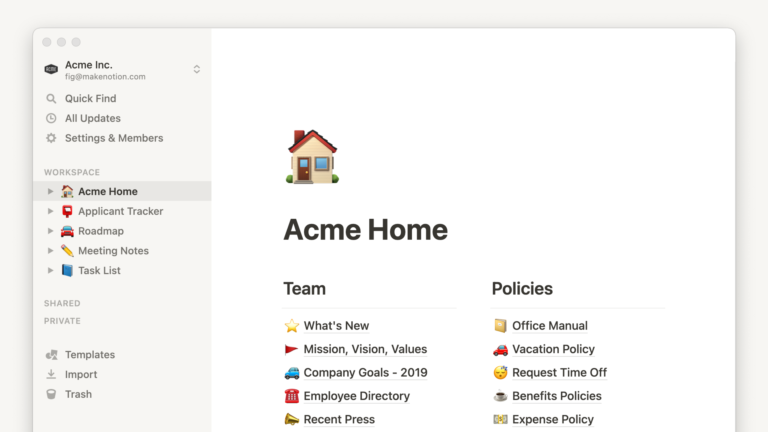
Notion is more than just a note-taking app. It often stores:
- Business strategies and roadmaps
- Client information and internal documents
- Login credentials and API keys (sometimes improperly stored)
- Personal journals and sensitive life details
Because of this concentration of valuable information, access to a single Notion account can be more damaging than access to several smaller tools combined. Cybercriminals understand this very well.
Why Login Pages Are Prime Targets for Attackers
Login pages are the gateway to digital identity. Attackers focus on them for three main reasons:
- They guarantee intent – Anyone visiting a login page is ready to enter credentials.
- They rely on habit – Users often log in quickly without verifying URLs.
- They bypass many defenses – Social engineering can defeat even strong technical security.
When users search for a platform’s login page instead of typing the official address directly, they increase their exposure to malicious results.
Notion Login: The Most Dangerous Check?
Why the Phrase “Notion Login” Attracts Threats
The exact phrase Notion login is frequently used in search engines. Cybercriminals exploit this behavior by creating:
- Fake websites that closely mimic the official Notion login page
- Sponsored ads that appear above legitimate results
- Look-alike domains with minor spelling differences
- Emails and messages urging users to “verify” or “re-login”
Because users expect a login page and are often in a hurry, they may not notice subtle warning signs. This makes the Notion login check one of the most dangerous routine actions a user can take online.
Common Attack Methods Linked to Notion Login
1. Phishing Websites
Fake login pages are the most common threat. They are designed to look nearly identical to the real Notion interface. Once credentials are entered, attackers capture them instantly and often redirect the user to the real site to avoid suspicion.
2. Search Engine Manipulation
Attackers optimize fake pages for search visibility or pay for ads that appear legitimate. Users who trust search results without scrutiny are especially vulnerable.
3. Email and Messaging Scams
Messages claiming unusual activity, expired sessions, or security upgrades often include links labeled “Notion login.” These links rarely lead where they claim.
4. Browser Extension Abuse
Malicious or compromised extensions can intercept login sessions, inject fake pop-ups, or redirect users to fake login screens.
The Real Consequences of a Compromised Notion Account
A stolen Notion login can lead to more than lost notes. Potential consequences include:
- Data leaks exposing confidential business or personal information
- Account takeover where attackers lock out the real owner
- Lateral attacks using information inside Notion to access other systems
- Identity theft if personal data is stored within workspaces
- Reputational damage for businesses and teams
In professional environments, one compromised account can escalate into a full organizational breach.
Psychological Triggers That Make Users Vulnerable
Cybercriminals don’t just rely on technology; they exploit human psychology. Common triggers include:
- Urgency: “Your account will be locked in 24 hours.”
- Authority: Messages appearing to come from official support.
- Routine: Logging in is a habit, not a conscious security check.
- Trust in branding: Familiar logos reduce suspicion.
When these triggers combine with a search for Notion login, the risk multiplies.
How to Identify a Fake Notion Login Page
Before entering credentials, users should always check:
- The full website address, not just the page design
- Secure connection indicators and consistent domain spelling
- Unexpected pop-ups asking for re-authentication
- Requests for information Notion normally does not ask for
Even one small inconsistency can indicate a trap.
Best Practices to Secure Your Notion Login
1. Bookmark the Official Login Page
Instead of searching every time, save the official login page and use it consistently.
2. Enable Two-Factor Authentication
This single step dramatically reduces the impact of stolen passwords.
3. Use a Password Manager
Password managers can detect fake websites and prevent auto-filling credentials on untrusted domains.
4. Avoid Logging In from Unknown Links
Never log in through links received via email, social media, or messaging apps unless you have verified their authenticity.
5. Monitor Account Activity
Regularly check for unfamiliar sessions, changes, or access logs if available.
Organizational Risks and Team Accounts
For teams, the danger of a compromised Notion login is even greater. Shared workspaces often include:
- Internal processes and documentation
- Client data and proposals
- Financial planning and strategic notes
One careless login can expose entire teams. Organizations should enforce security training, access controls, and regular audits to minimize risk.
Why This Risk Is Growing, Not Shrinking
Despite improved security technology, login-related attacks are increasing because:
- Remote work has expanded attack surfaces
- Users rely more heavily on cloud platforms
- Attack tools have become easier and cheaper to deploy
- People trust familiar brands too easily
As long as users continue to search and click without verifying, the Notion login threat will remain significant.
Building Safer Digital Habits
Security is not just about tools; it is about behavior. Safer habits include:
- Slowing down before entering credentials
- Treating every login as a security decision
- Questioning unexpected prompts
- Educating yourself and your team regularly
These habits cost nothing but can prevent devastating losses.
Conclusion: Awareness Is the Strongest Defense
The phrase Notion login may seem harmless, but it represents a critical point of vulnerability in today’s digital environment. Its familiarity, frequency, and importance make it a prime target for cybercriminals. Understanding why this simple check can be dangerous empowers users to take control of their security